Our Portfolio
Two platforms.
One
edge.
NuajProtect secures your network edge today. NexaCloud orchestrates your cloud next.
NuajProtect
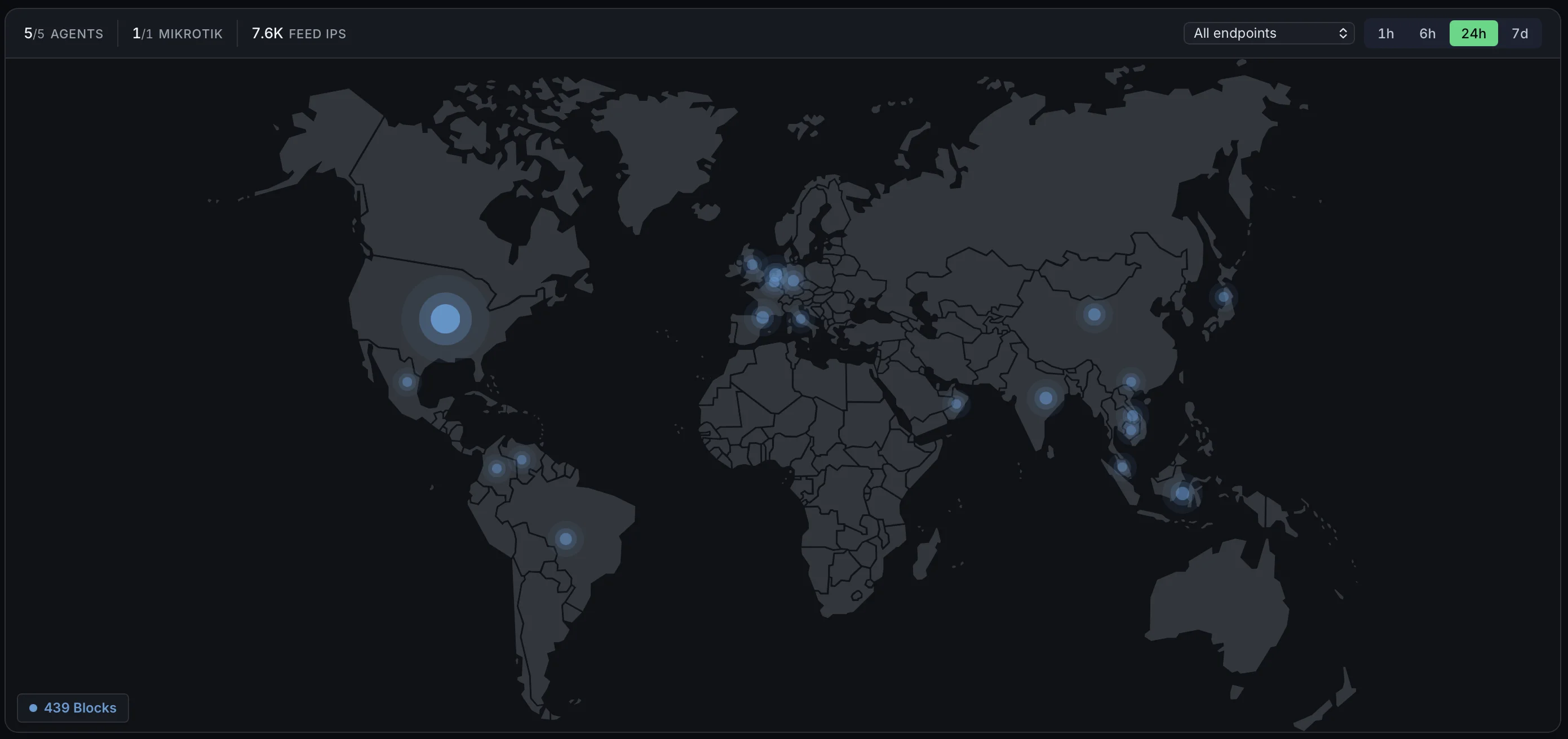
Every network is under constant attack. NuajProtect blocks malicious traffic at the edge — before it ever reaches your applications — with live threat intelligence enforced in the kernel at line rate. One defense across Linux servers, MikroTik routers, and transparent bridge appliances.
NexaCloud Coming 2027
Your servers are capable of far more. NexaCloud turns bare metal into a self-service, multi-tenant cloud — automated provisioning, metered billing, zero manual ops. The natural next step once NuajProtect secures your edge.
How NuajProtect Works
Cyberattacks stopped at the edge,
in three steps.
A live picture of global attack activity, enforced inside your kernel at line rate — no proxy, no latency penalty, no blocklists to hand-write.
Global threat intelligence
NuajProtect continuously identifies malicious IPs, botnets, and cyberattack infrastructure, then distributes that intelligence to every protected edge in near real time.
Fast-path kernel blocking
Verdicts are enforced in the kernel — XDP/eBPF on Linux, native rules on MikroTik — dropping malicious packets at line rate before they ever reach your applications.
Enforced everywhere
Deploy as a Linux agent, a MikroTik integration, or a transparent bridge appliance. One policy, applied consistently across servers, routers, and network segments.
Engineering Philosophy
Built for operators,
by
operators.
Performance First
We write code that respects your hardware. Our fast-path processing ensures microsecond latencies even under heavy multi-gigabit traffic loads.
Uncompromising Architecture
Zero proprietary lock-in. We build tools that integrate natively into your existing Linux, MikroTik, and Proxmox infrastructure layers seamlessly.
Data Sovereignty
You own your operations. We design our platforms to support fully self-hosted, air-gapped, and privacy-first deployments worldwide.
Questions
Everything you need
to know.
What is NuajProtect?
What platforms does it run on?
How is it different from a traditional firewall?
Will it slow down my network?
Is it self-hosted or SaaS?
How do I get access?
Why we built it
I ran a data center for 15 years. One day I really looked at what was hitting the edge. Every server was under attack, several times a second, all day, every day. Nothing out there stopped it the way it should. So I built NuajProtect.
— Antoine Boucher, Founder
Why Nuaj
Modern IT has become
unnecessarily complicated.
More vendors. More products. More dashboards. More security alerts. More things to break — and IT teams spending more time managing technology than using it to move the business forward. Nuaj exists to change that.
We build infrastructure and cybersecurity solutions that reduce complexity, improve visibility, and strengthen operations. No unnecessary features. No unnecessary complexity. No unnecessary overhead — just practical platforms that help organizations operate securely, efficiently, and at scale.
Because technology should be an advantage, not a burden.